- ESET Research examined the operations of Russia-aligned advanced persistent threat (APT) group Gamaredon, which is currently the most engaged APT group in Ukraine.
- The majority of Gamaredon’s cyberespionage attacks are directed against Ukrainian governmental institutions.
- ESET saw a few attempts to compromise targets in several NATO countries - namely Bulgaria, Latvia, Lithuania, and Poland - but no successful breaches were observed.
- Gamaredon notably improved its cyberespionage capabilities, and developed several new tools in PowerShell, with a focus on stealing valuable data – from email clients, instant messaging applications such as Signal and Telegram, and web applications running inside internet browsers.
- ESET Research discovered PteroBleed, an infostealer that also focuses on stealing data from Delta – a system developed by the Ukrainian Ministry of Defence.
BRATISLAVA — September, 2024 — ESET Research examined the operations of Gamaredon, a Russia-aligned APT group that has been active since at least 2013 and is currently the most engaged APT group in Ukraine. Gamaredon has been attributed by the Security Service of Ukraine (SSU) to the Russian 18th Center of Information Security of the FSB, operating out of occupied Crimea. ESET believes this group to be collaborating with another threat actor that ESET Research discovered and named InvisiMole. The majority of Gamaredon’s cyberespionage attacks are directed against Ukrainian governmental institutions. However, in April 2022 and February 2023, ESET also saw a few attempts to compromise targets in several NATO countries, namely Bulgaria, Latvia, Lithuania, and Poland, but no successful breaches were observed.
Gamaredon is using ever-changing obfuscation tricks and numerous techniques used for bypassing domain-based blocking. These tactics pose a significant challenge to tracking efforts, as they make it harder for systems to automatically detect and block the group’s tools. Nevertheless, during ESET’s investigation, ESETresearchers managed to identify and understand these tactics and kept track of Gamaredon’s activities. The group has been methodically deploying its malicious tools against its targets since well before the invasion began. To compromise new victims, Gamaredon conducts spearphishing campaigns and then uses its custom malware to weaponise Word documents and USB drives accessible to the initial victim, expecting them to be shared with further potential victims.
During 2023, Gamaredon notably improved its cyberespionage capabilities, and developed several new tools in PowerShell, with a focus on stealing valuable data – from email clients, instant messaging applications such as Signal and Telegram, and web applications running inside internet browsers. However, PteroBleed, an infostealer ESET discovered in August 2023, also focuses on stealing data related to Delta – a system developed by the Ukrainian Ministry of Defence for collecting, processing, and displaying information about enemy forces – and from the webmail service used by the Ukrainian Ministry of Defence.
“Gamaredon, unlike most APT groups, does not try to be stealthy and remain hidden as long as possible by using novel techniques while conducting cyberespionage operations, but rather, the operators are reckless and do not mind being discovered by defenders during their activities. Even though they do not care so much about being noisy, they still put in a lot of effort to avoid being blocked by security products and try very hard to maintain access to compromised systems,” explains ESET researcher Zoltán Rusnák, who investigated Gamaredon.
“Typically, Gamaredon attempts to preserve its access by deploying multiple simple downloaders or backdoors simultaneously. The lack of sophistication of Gamaredon tools is compensated by frequent updates and the use of regularly changing obfuscation,” adds Rusnák. “Despite the relative simplicity of its tools, Gamaredon’s aggressive approach and persistence make it a significant threat. Given the ongoing war in the region, we expect Gamaredon to continue in its focus on Ukraine,” he concludes.
For a more detailed analysis and technical breakdown of Gamaredon’s tools and activities, check out the latest ESET Research white paper “Cyberespionage the Gamaredon way: Analysis of toolset used to spy on Ukraine in 2022 and 2023 ” on WeLiveSecurity.com. Make sure to follow ESET Research on Twitter (today known as X) for the latest news from ESET Research.
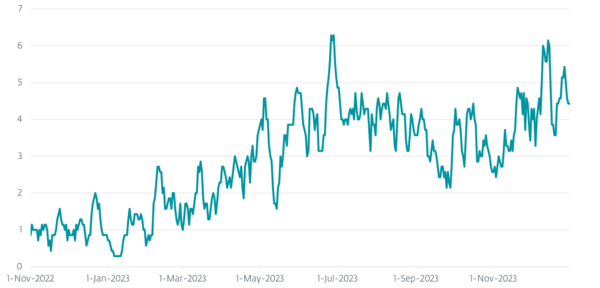
Seven-day moving average of unique machines attacked in Ukraine