1bn+
users worldwide
400k+
business customers
ESET Endpoint Security for Windows
Leverages a multilayered approach that utilizes multiple technologies in dynamic equilibrium to constantly balance performance, detection and false positives enabling organizations to:

Protect against ransomware

Block targeted attacks

Prevent data breaches

Stop fileless attacks

Detect advanced persistent threats
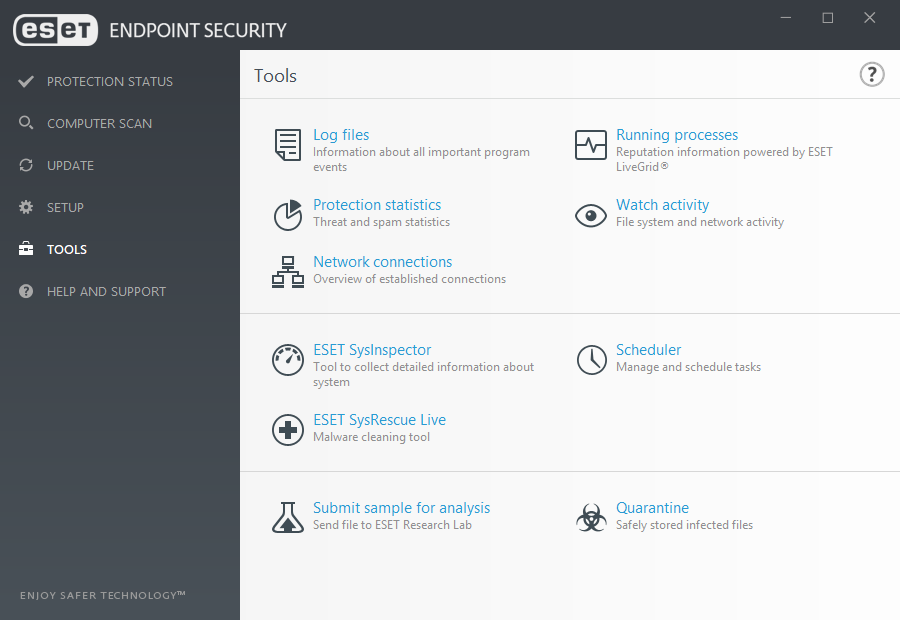
Management server
ESET Security Management Center manages endpoint products from a single pane of glass and can be installed on Windows or Linux. As an alternative to on-premise installation, customers with up to 250 seats can manage their endpoints via ESET Cloud Administrator.
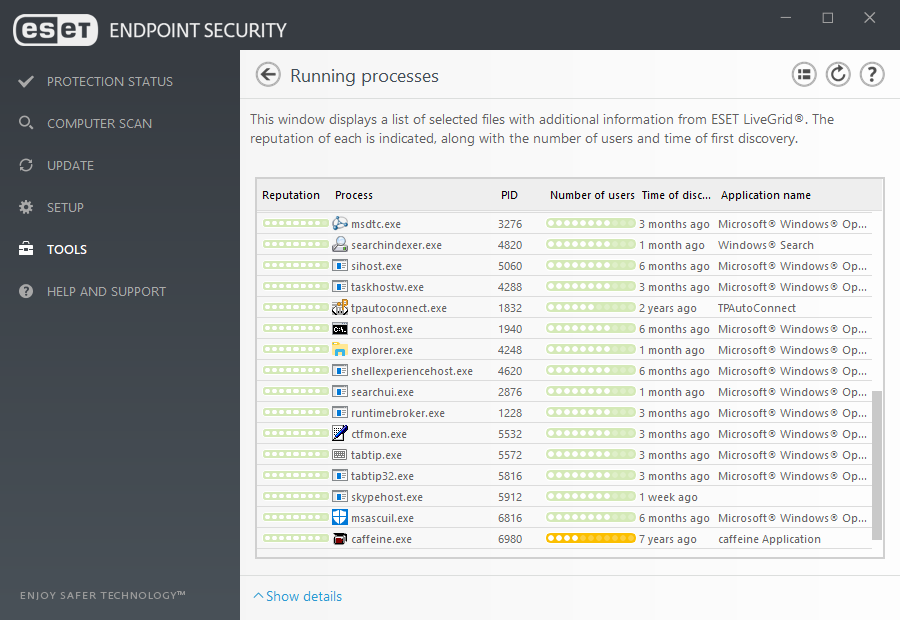
Machine learning
All ESET Endpoint products currently use machine learning in conjunction with all of our other layers of defense and have done so since 1997. Specifically, machine learning is used in the form of consolidated output and neural networks. For a deep inspection of the network, admins can turn on the special aggressive machine learning mode that works even without internet connection.
Multilayered defense
A single layer of defense is not enough for today's evolving threat landscape. All ESET’s endpoint products have the ability to detect malware pre-execution, during execution and post-execution. Focusing on the whole of the malware lifecycle, not just on a specific part, allows ESET to provide the highest level of protection possible.
Use cases
PROBLEM
Some businesses require extra insurances that they will be protected from ransomware attacks.
SOLUTION
- Network Attack Protection has the ability to prevent ransomware from ever infecting a system by stopping exploits at the network level.
- Our multilayered defense features an in-product sandbox that has the ability to detect malware that attempts to evade detection by using obfuscation.
- Leverage ESET’s cloud malware protection system – LiveGrid® - to automatically protect against new threats without the need to wait for the next detection update.
- All products contain protection in the form of Ransomware Shield to ensure that businesses are protected from malicious file encryption.

protected by ESET since 2017
more than 9,000 endpoints

protected by ESET since 2016
more than 32,000 endpoints
The ESET difference
Behavioral Detection - HIPS
ESET's Host-based Intrusion Prevention System (HIPS) monitors system activity and uses a pre-defined set of rules to recognize and stop suspicious system behavior.
Ransomware Shield
An additional layer protecting users from ransomware. Our technology monitors and evaluates all executed applications based on their behavior and reputation. It is designed to detect and block processes that resemble behavior of ransomware.
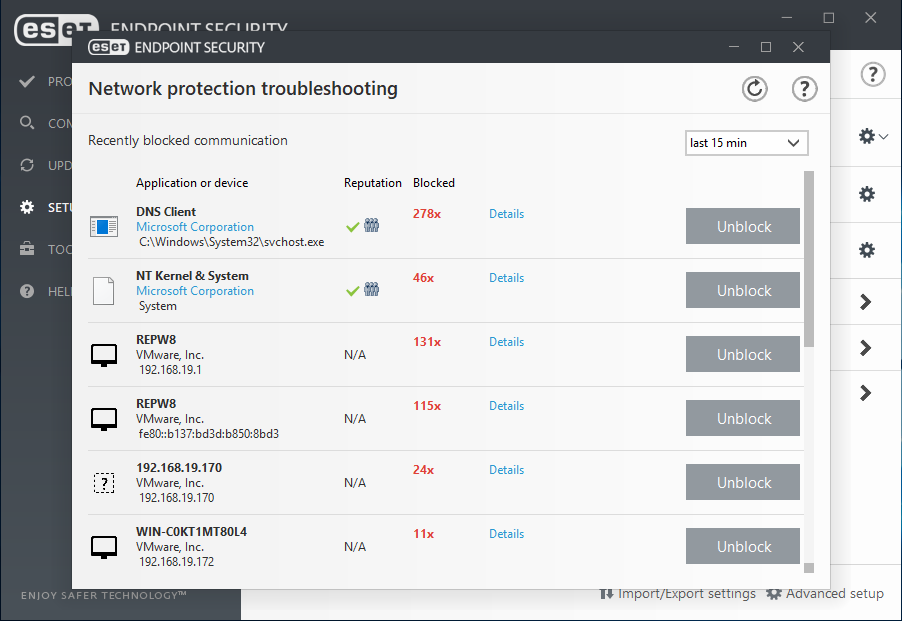
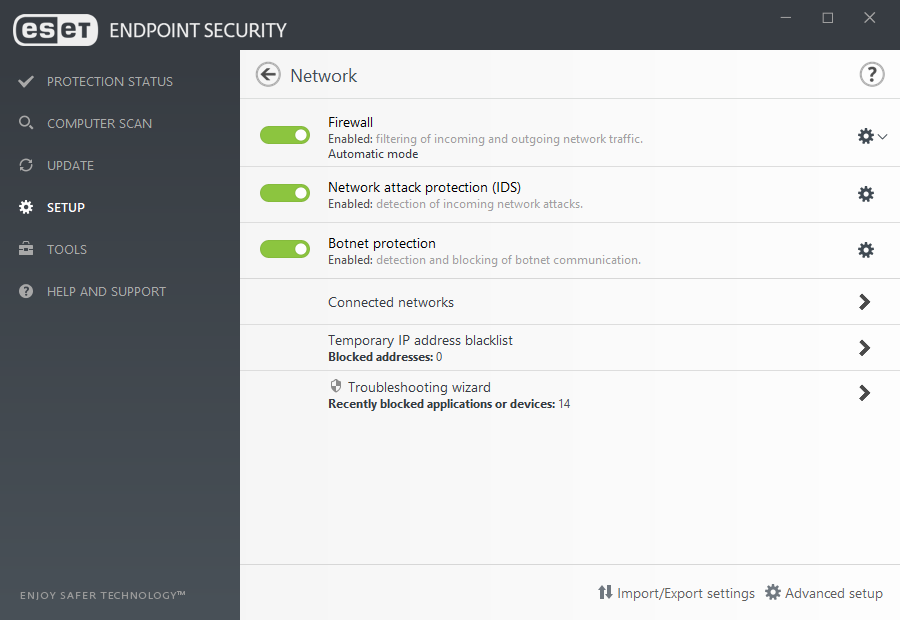
Network Attack Protection
ESET Network Attack Protection improves detection of known vulnerabilities on the network level. It constitutes another important layer of protection against spreading malware, network-conducted attacks, and exploitation of vulnerabilities, for which a patch has not yet been released or deployed.
Advanced Memory Scanner
A unique ESET technology which effectively addresses an important issue of modern malware – heavy use of obfuscation and/or encryption. Advanced Memory Scanner monitors the behavior of a malicious process and scans it once it decloaks in memory.
In-product Sandbox
ESET’s in-product Sandbox assists in identifying the real behavior hidden underneath the surface of obfuscated malware. Utilizing this technology, ESET solutions emulate different components of computer hardware and software to execute a suspicious sample in an isolated virtualized environment.
Exploit Blocker
ESET Exploit Blocker monitors typically exploitable applications (browsers, document readers, email clients, Flash, Java, and more) and instead of just aiming at particular CVE identifiers, it focuses on exploitation techniques. When triggered, the threat is blocked immediately on the machine.
Two-way firewall
Prevents unauthorized access to the company network. It provides anti-hacker protection, data exposure prevention, and enables defining trusted networks, making all other connections, such as to public Wi-Fi, restricted by default.
Botnet Protection
ESET Botnet Protection detects malicious communication used by botnets, and at the same time identifies the offending processes. Any detected malicious communication is blocked and reported to the user.

ESET #1 in AV Comparatives Performance test in May 2019.

ESET achieved highest score in SE Labs test in Q1 2019.

ESET Endpoint Security named best business antivirus for MacOS.

ESET ranked highest by final score in VBSpam test in June 2019.
ESET ENDPOINT SECURITYFOR WINDOWS
Make an enquiry
Leave us your contact details to receive an offer tailored to your company's needs.
Try before you buy
Why not download a free trial license with absolutely no commitment on your side.
System Requirements
Looking for the complete security of your network?
Related enterprise-grade solutions
ESET Dynamic Endpoint Protection
- Security Management Center
- Endpoint Protection Platform
- Cloud Sandbox Analysis
ESET Targeted Attack Protection
- Security Management Center
- Endpoint Protection Platform
- Cloud Sandbox Analysis
- Endpoint Detection & Response
Related SMB solutions
ESET Endpoint Protection Advanced Cloud
- Cloud Administrator
- Endpoint Security
- File Server Security
ESET Secure Business
- Security Management Center
- Endpoint Security
- File Server Security
- Mail Security
Stay on top of cybersecurity news
Brought to you by awarded and recognized security researchers from ESET's 13 global R&D centers.