What is ransomware?
This specific kind of malicious software is used for extortion. When a device is successfully attacked, malware blocks the screen or encrypts data stored on the disk and a ransom demand with payment details is displayed to the victim.
How to recognize ransomware?
If you have been attacked, ransomware will in most cases inform you by displaying a ransom message on your screen, or by adding a text file (message) to the affected folders. Many ransomware families also change the file extension of the encrypted files.

How does ransomware work?
There are multiple techniques used by the ransomware operators:
- Diskcoder ransomware encrypts the whole disk and prevents the user from accessing the operating system.
- Screen locker blocks the access to the device’s screen.
- Crypto-ransomware encrypts data stored on victim’s disk.
- PIN locker targets Android devices and change their access codes to lock out their users.
Read more
How to stay protected?
Basic rules you should follow to avoid your data being lost:
- Back up your data on a regular basis – and keep at least one full backup off-line
- Keep all your software – including operating systems – patched and up to date
However to help users/organizations recognize, prevent and remove ransomware a reliable and multi-layered security solution is the most efficient option.
Advanced rules mainly for businesses:
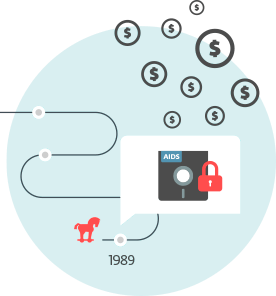
Brief history
The first documented case of ransomware was in 1989. Called the AIDS Trojan, it was physically distributed through the post via thousands of floppy disks that claimed to contain an interactive database on AIDS and risk factors associated with the disease. When triggered, the malware effectively disabled the user's access to much of the content on the disk.
AIDS Trojan demanded ransom (or as the ransom note named it, “license payment”) of US $189 to be sent to a post office box in Panama allowing the user to execute the program 365 times. Dr. Joseph Popp was identified as the author; authorities, however, declared him mentally unfit to stand trial.




